AWS CONNECTIVITY OPTIONS – CHOOSING THE RIGHT TOOL FOR THE JOB

Datacenter and cloud architectures are increasingly bespoke. As new technologies and types of environments arise, so do new tools from cloud providers. Today’s digital architects have an overwhelming number of solutions for each use case they encounter, including connectivity options.
So how do architects choose a connectivity option for peak performance, security, availability, and cost?
Because cloud architecture is not only a science but an art, the answer is, “it depends.” It depends on the use case and connectivity goals. It depends on the business goals, roadmap for cloud adoption, urgency to modernize, and staffing expertise. It can be difficult to determine which solution is right for each situation.
In this article, we’ll cover the benefits and limits of seven AWS connectivity options to help you choose the best fit for any situation.
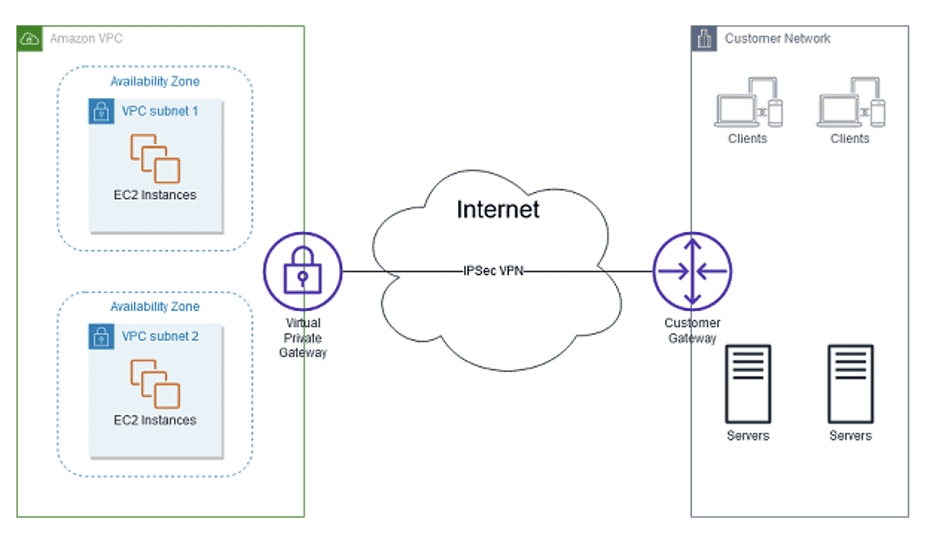
AWS Native VPN
AWS Native VPN is an IPsec connection over the Internet from on-premises remote networks to an Amazon VPC. It’s beneficial when you want to reuse existing VPN resources and Internet connections. It can also be a critical component when you want to use a VPN as a backup for Direct Connect.
Key points to note:
- VPN does not support Equal Cost Multi Path (ECMP) for egress data path, when multiple AWS Native VPN tunnels terminate on the same Virtual Private Gateway.
- AWS Native VPN’s network performance is entirely dependent on latency, variability, and availability of the internet connection. Ensure that your application’s bandwidth requirements are appropriately measured.
- While VPN configuration results in two tunnels, the business (not AWS) is responsible for implementing redundancy and failover.
- In this case, VPN will support a much smaller bandwidth than Direct Connect.
Below we’ll cover two of the many different ways to combine VPN with other AWS native networking constructs.
AWS Site-to-Site VPN
Site-to-Site VPN is the most cost-effective option for creating connectivity from on-premises to AWS cloud. You can configure your existing firewall, either software or hardware, on the on-premises network as a Customer Gateway Device. The device can now be configured to work with Site-to-Site VPN connection to AWS through the console. AWS Console provides documentation for varied Customer Gateway Devices, including Cisco, F5 Networks, and Fortinet.
Key point to note:
- Site-to-Site configuration is generally used to connect to one VPC.
AWS Transit Gateway with VPN
This approach is optimal for a scalable VPN to connect multiple VPCs and customer edge devices on-premises and create VPN IPSEC tunnels. You can use AWS native tools to configure Transit Gateway VPN attachment. On the AWS end, create a VPN attachment through AWS’s VPC service portal. The benefit of this configuration is allowing native attachments to act as a hub to multiple VPCs.
Key points to note:
- Native tunnels like these are designed for basic connectivity use cases, so advanced features such as policy match, IP address masking, traffic inspection, advanced firewall analysis, etc. are not supported.
- ECMP is supported when terminating at Transit Gateway.
(Source: AWS)
AWS Direct Connect
Direct Connect (DX) is a dedicated, private fiber connection to AWS. It allows you to connect an on-premise router to an AWS DX router over 1-gigabit or 10-gigabit ethernet fiber optic cable. However, some have opted for hosted connections to support smaller bandwidth (i.e. 50Mbps, 100Mbps, 200Mbps, 300Mbps, 400Mbps, 500Mbps, 1GBps, 2Gbps, 5Gbps), that can be ordered through approved AWS Direct Connect Partners.
DX is optimal for private connectivity to Amazon VPC, EC2, S3 and DynamoDB using virtual interfaces, bypassing internet service providers in your network path. It provides more consistent network performance and lower cost data-out rates compared to the Internet.
Key points to note:
- For billing purposes, make sure to budget for port-hours used in addition to data transfer rates.
- DX is a single, non-redundant connection. For redundancy, consider dual DX connections or AWS Managed VPN option.
- Maximum number of links in a Link Aggregation groups is four, for dedicated 1GBps and 10GBps connections only.
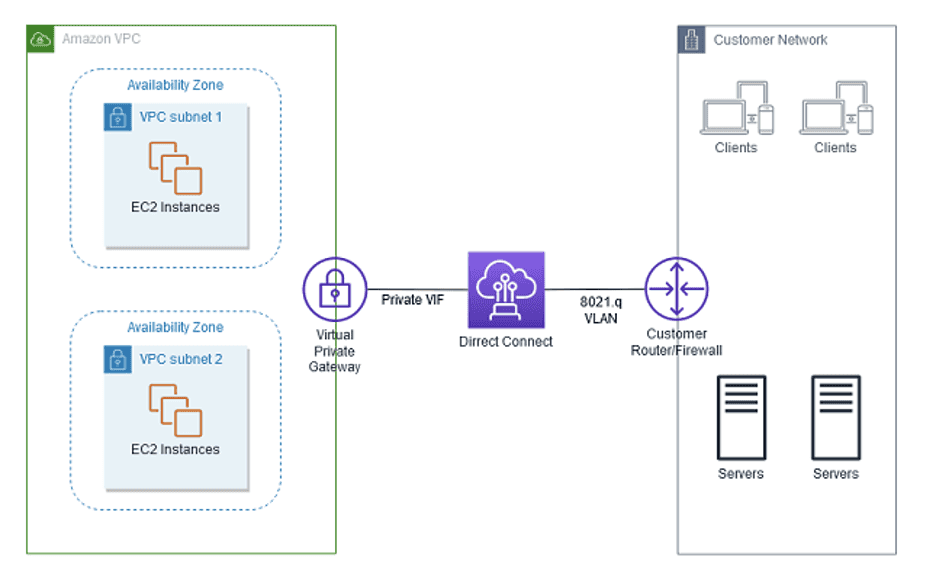
(Source: AWS)
AWS Direct Connect Gateway
While Direct Connect is an optimal solution for connectivity from on-premises to AWS resources, it is a single non-redundant connection. Conversely, Direct Connect Gateway is a globally available resource. With DX gateway, you can connect multiple DX connections over private VIF to one or more VPCs in your account located in the same or different regions. DX gateway is a grouping of Virtual Private Gateways and Private VIFs. You can associate DX gateway with a virtual private gateway from connections at any DX location
DX gateway is best when there is a need to interface with multiple VPCs in any AWS region (except AWS China) or when you need to share private VIFs to interface with up to 10 VPCs. This allows reduction of BGP sessions between on-premises network and AWS deployment.
Key points to note:
- Keep an eye on the cost model for DX gateway. The user is billed per port hour and egress data charges depending on the location.
- The billing begins 90 days after a connection is created, or after the connection is established between on-premises router and AWS router (whichever comes first).
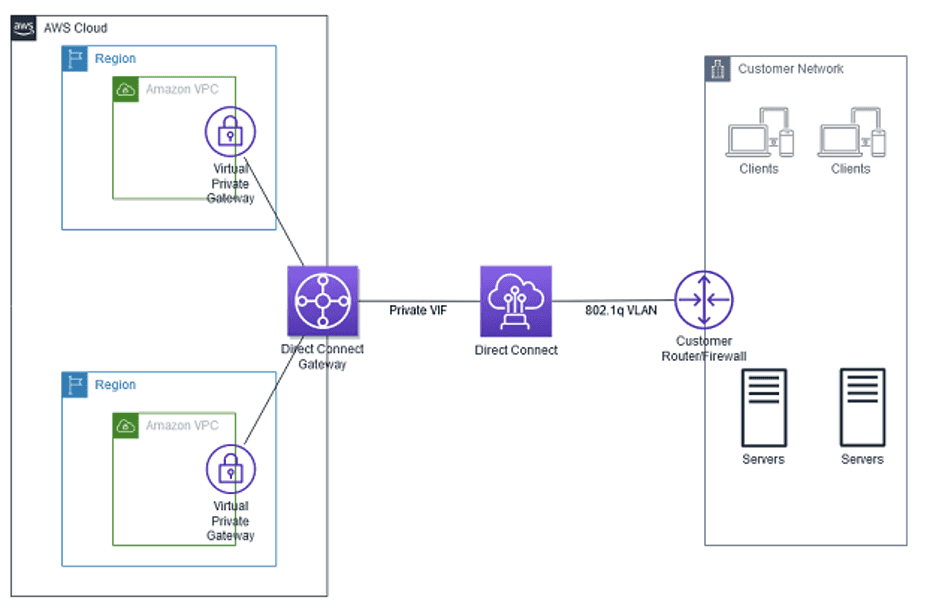
(Source: AWS)
AWS Transit Gateway
As workloads grow on AWS, scaling networks across multiple accounts and VPCs can incur management and cost overhead, even if VPC peering is utilized. Transit Gateway is a service that allows you to connect multiple VPCs with on-premises networks to a single connection from a central gateway. It can act as a hub that controls how traffic is routed across connected networks which act like spokes.
AWS users leverage Transit Gateway for simplified management and reduced operational costs, since each network must only connect to Transit Gateway, as opposed to every other network. Since scaling is critical in enterprise accounts, as each new VPC connected to Transit Gateway can be automatically available to every other connected network. It’s also important to note that TGW supports multicast and inter-regional peering.
Key point to note:
- AWS Transit Gateway Connect does not support static routes for external connectivity. BGP is a minimum requirement.
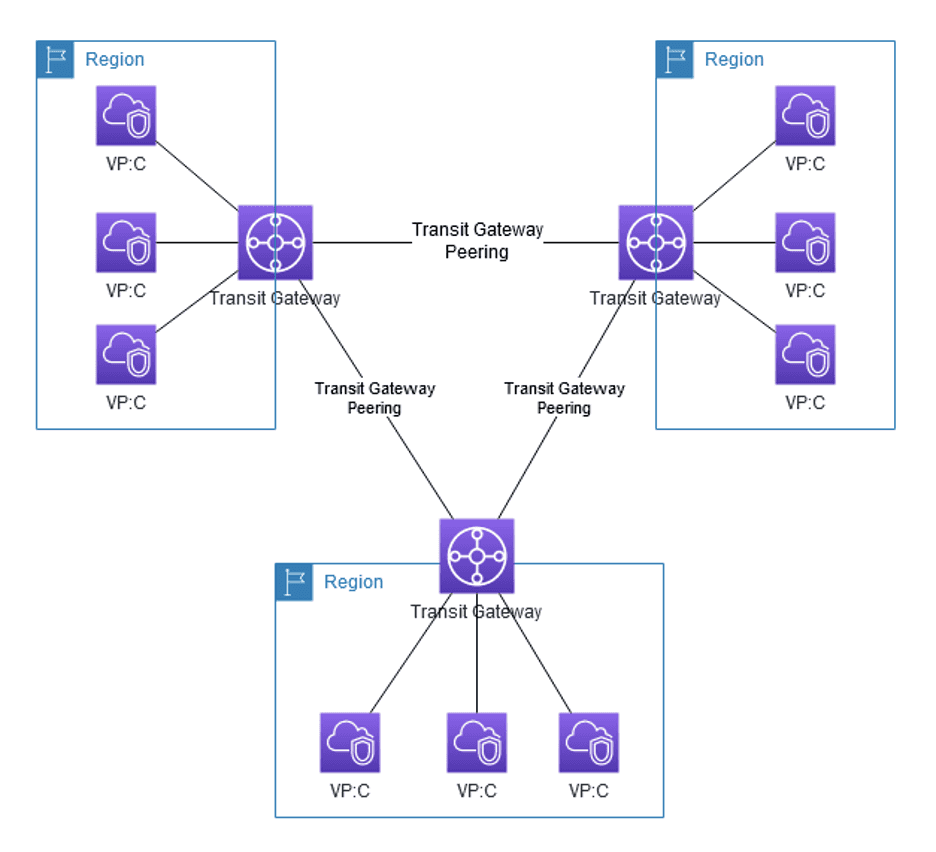
(Source: AWS)
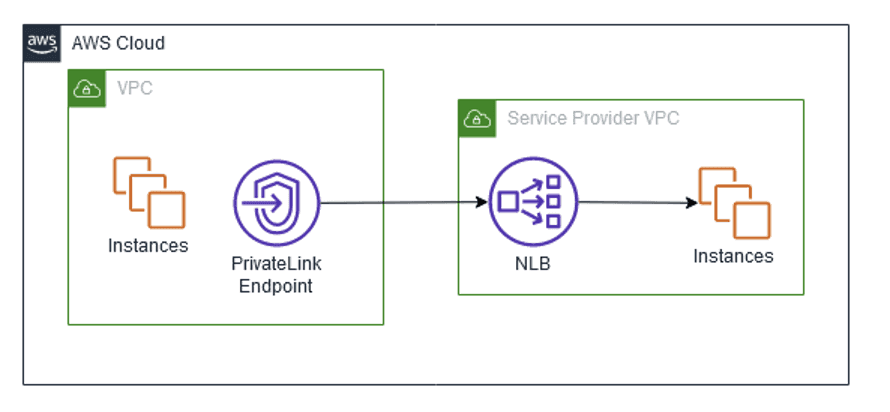
AWS PrivateLink
PrivateLink enables private connectivity between VPCs, on-premises applications, and other AWS services, securely on the Amazon network. It is a simplified private connectivity between accounts and VPCs under an organization without configuring firewall rules, path definitions, or route tables. The private connectivity function negates a requirement for Internet Gateway or VPC peering connection.
Users can leverage services from another VPC within the AWS network, in a highly scalable, one-to-many topology. Since multiple endpoint services can be accessed, PrivateLink can benefit from the elastic load balancing and hourly endpoint cost model.
Key points to note:
- A key benefit here is that you can use overlapping CIDRs.
- PrivateLink can span VPCs and accounts, allowing the offer of services to consumers from other accounts without additional inter-connectivity.
(Source: AWS)
AWS Connectivity Options Service Limits Cheat Sheet:
| Service | Limits |
| AWS Native VPN | -Supports up to 1.25 Gbps throughput per VPN tunnel -4 links for Link Aggregation Groups -Advertise up to 100 routes |
| AWS Site-to-Site VPN | -Supports up to 50 Customer Gateways, and 50 Site-to-Site VPN connections per Region |
| AWS Transit Gateway with VPN | -Maximum 5 transit gateway attachments per VPC |
| AWS Direct Connect | -Advertise up to 100 routes over each Border Gateway Protocol session |
| AWS Direct Connect Gateway | -Connect up to 5,000 VPCs and on-prem environments through a single gateway Multi-account support allows associating up to 10 VPCs or up to 3 AWS Transit Gateways from multiple AWS accounts |
| AWS Transit Gateway | -Regional scalability as a network hub for up to 5,000 attachments |
| AWS PrivateLink | -Default bandwidth for each interface endpoint supports up to 10 Gbps per Availability Zone, bursting up to 40Gbps |
Clearly, there are a significant number of factors to consider when choosing a connectivity approach. The best place to start is to identify your use case, understand the current landscape, and prioritize goals. Subsequently, identify requirements of the most critical goals and align with organizational spend. Based on these vectors, develop a phased approach with rollback plans. Remember that cloud adoption is a journey.
