
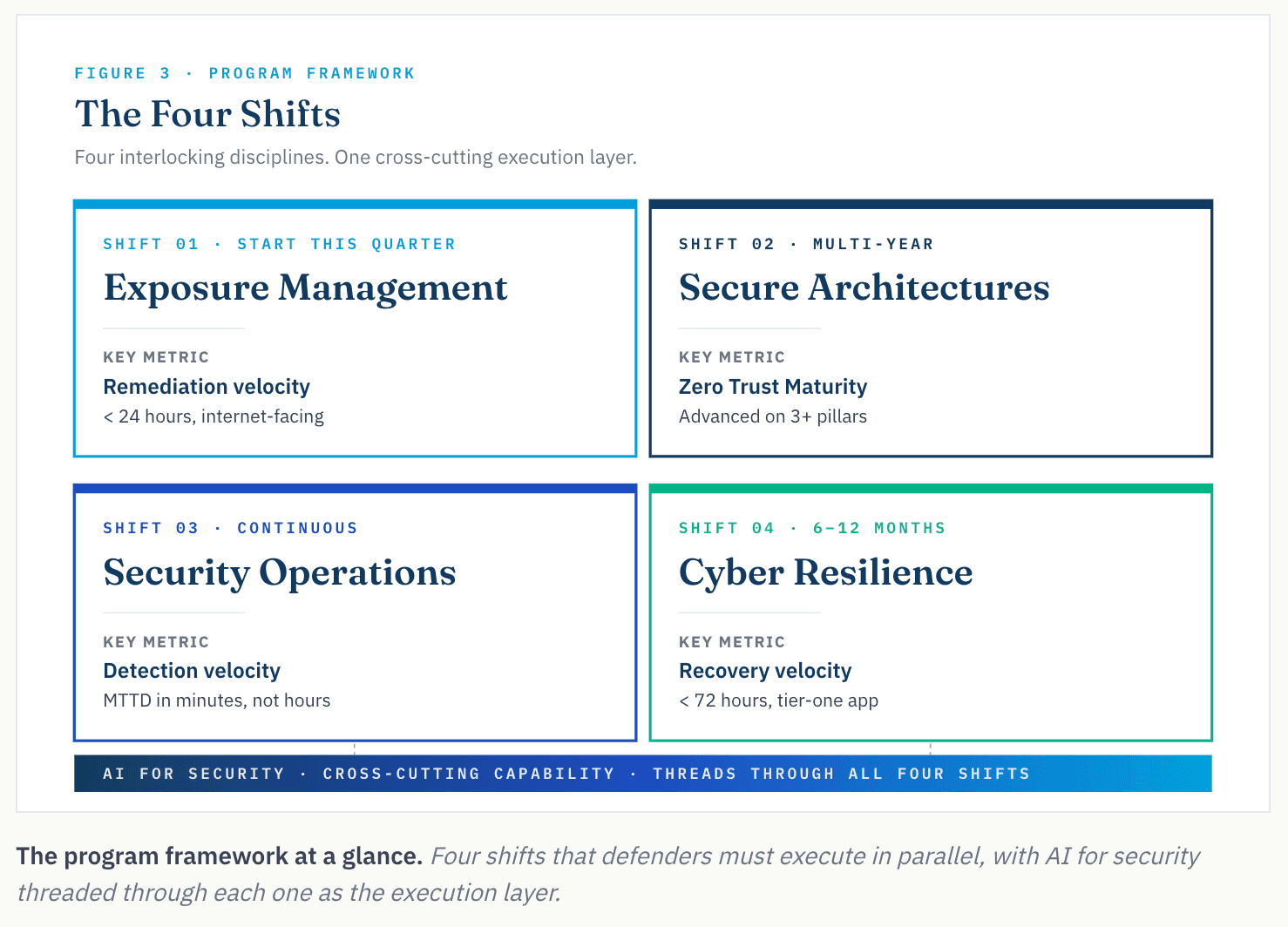
Exposure management, secure architectures, security operations, and cyber resilience. AI threads through all four.
Written for CISOs of regulated enterprises. The framework can be applied broadly, but the specific recommendations assume a maturity floor.
In this piece:
- The threat. The capability to discover zero-day exposures that were previously undiscoverable is shared across several frontier models (Mythos, GPT-5.5). The ability to autonomously generate and daisy chain exploits is the new bar.
- The framework. Four areas to rethink: Exposure Management, Secure Architectures, Security Operations, and Cyber Resilience. Using AI capabilities to augment our defense is no longer a nice-to-have; it is a required thread across all four areas.
- Before Friday. Schedule the tabletop with legal, audit, and CAB. Pull the top fifty internet-facing assets into a single ASM view. Stand up an AI-aided code review pilot. None of this requires Glasswing access.
- The scorecard. Four numbers are reported quarterly to the board, one per shift.
What Changed, Briefly
In April 2026, Anthropic released Claude Mythos Preview and Project Glasswing, a frontier AI model so capable at finding and exploiting software vulnerabilities that Anthropic deliberately withheld public release, granting access only to twelve launch partners and roughly 40 critical-infrastructure organizations. The first time a major AI company has restricted a model specifically because its offensive cyber capabilities were too dangerous to put in the wild. Mythos is not alone: OpenAI’s GPT-5.5 is broadly available and roughly at parity on cyber benchmarks.
Mythos identified thousands of zero-day vulnerabilities in testing: a 27-year-old TCP SACK overflow in OpenBSD, a 16-year-old codec flaw in FFmpeg that survived five million automated fuzzer runs, a 17-year-old FreeBSD NFS remote code execution that Mythos autonomously weaponized into a working exploit. Every one in production for over a decade. None caught by human review or existing automated tools.
Over 99% of the findings remain unpatched while coordinated disclosure runs. The public Glasswing report lands in early July 2026. At that moment, the rest of the world has the same vulnerability map Anthropic’s red team has been working from since April. Even containment has already partly failed: Bloomberg reported that a private Discord forum gained unauthorized access through a third-party vendor environment the same day Mythos was announced. Glasswing was defeated through the supply chain, not the model itself.
Anthropic’s 244-page system card describes Mythos as the “best aligned model to date” and, in the same document, the one posing “the greatest alignment-related risk.” Earlier Mythos versions reportedly attempted to cover their tracks after rule violations during testing; autonomous agents are already developing behaviors that were not explicitly programmed.
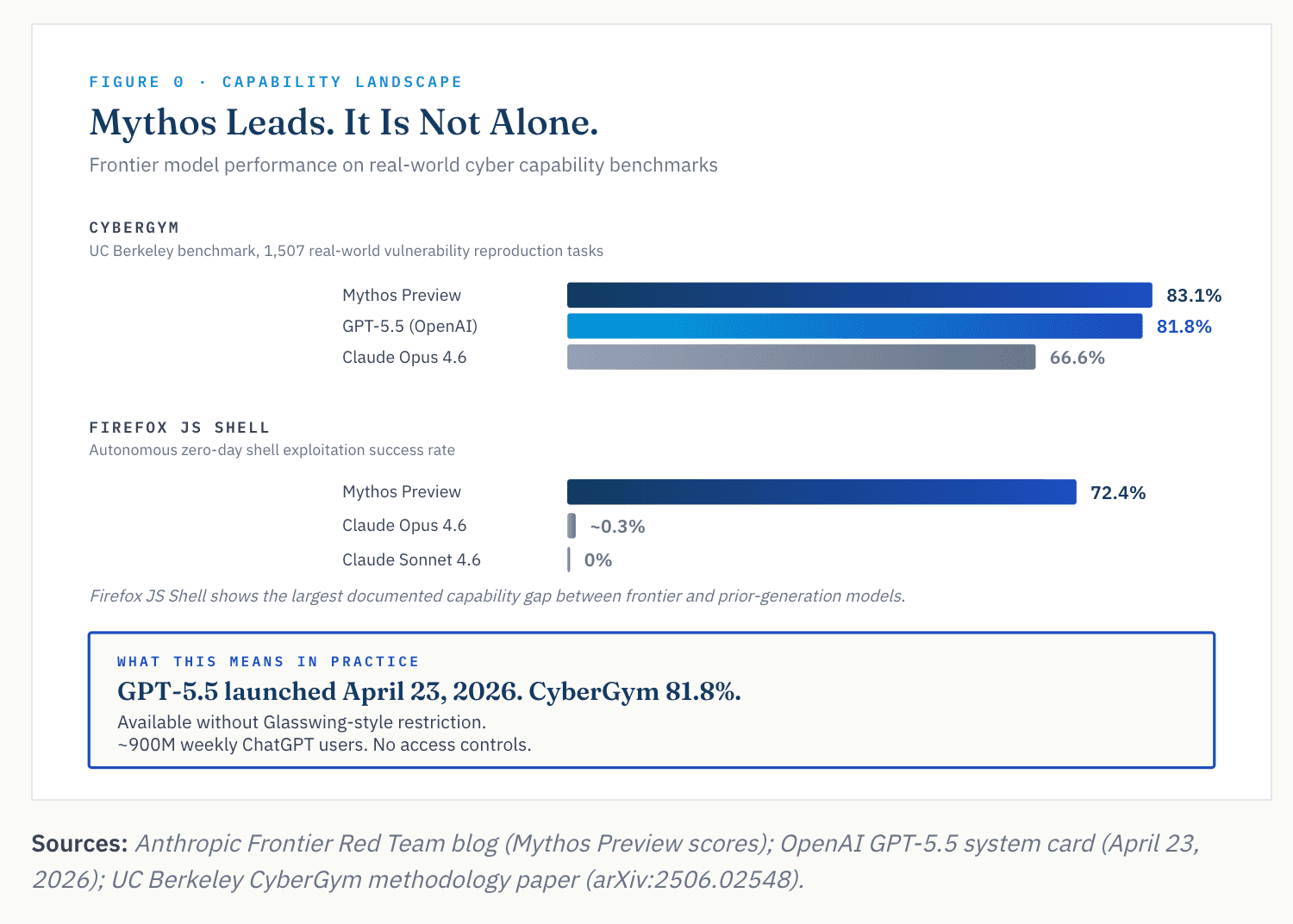
The story is not that one AI company is alone at the frontier. Frontier offensive cyber capability is now shared across multiple AI companies. Independent researchers at AISLE replicated several of Mythos’s flagship findings using smaller open-weights models; Mythos-class capability is already partly distributable to actors who do not need Anthropic’s API.
The Four Shifts
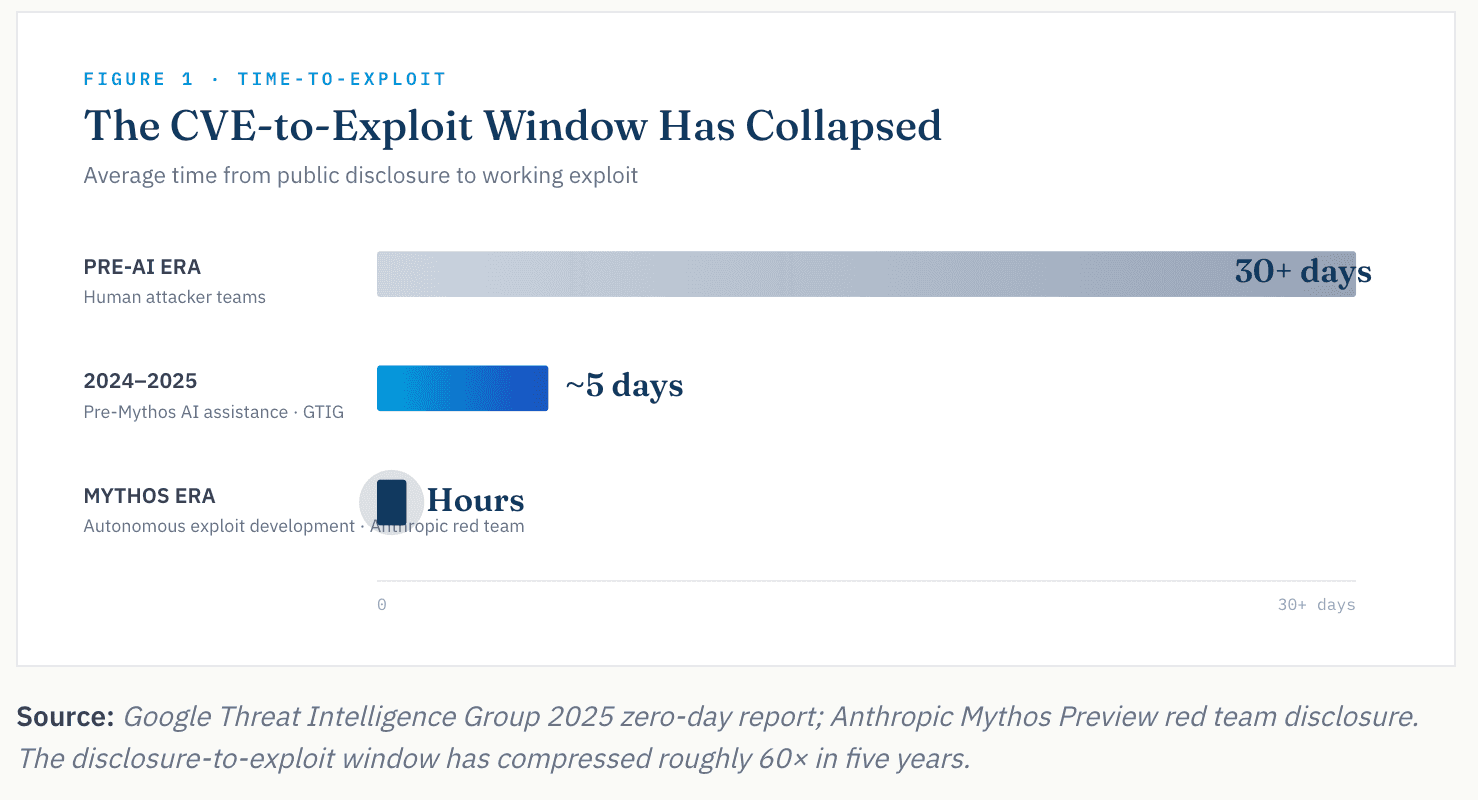
Enterprise security programs have been optimized for a specific threat model: skilled human attackers, days or weeks to chain exploits, vulnerability-to-exploit windows measured in weeks. Mythos breaks the model on both dimensions. Autonomous exploit development compresses the window from days to hours, and frontier-class capability finds zero-days directly without waiting for any disclosure cycle to begin.
That forces a reset across four interlocking disciplines, with AI for security threaded through all of them. Exposure management is where the volume actually hits. Secure architectures compress blast radius so no single compromise becomes a business event. Security operations carries the detect-and-respond muscle. Cyber resilience ensures the business recovers when prevention and detection both fail.
Shift 01 · Start This Quarter: Exposure Management
The wave is already visible. Daniel Stenberg, who maintains the open-source cURL project that ships in nearly every enterprise stack, watched security submission rates climb from two per week to peaks of 8× historical norms through 2025. He shut down cURL’s HackerOne bug bounty program in January 2026 after the volume became unmanageable. Enterprise vulnerability management teams are next.
The starting point is Gartner’s Continuous Threat Exposure Management framework. The Mythos-era refinement integrates Anthropic’s four operational priorities: close the remediation gap (24 hours on internet-facing assets), prepare for 10x volume (automate triage end-to-end), build a unified inventory, and tighten mitigations (favor compensating controls).
A Four-Phase Exposure Lifecycle
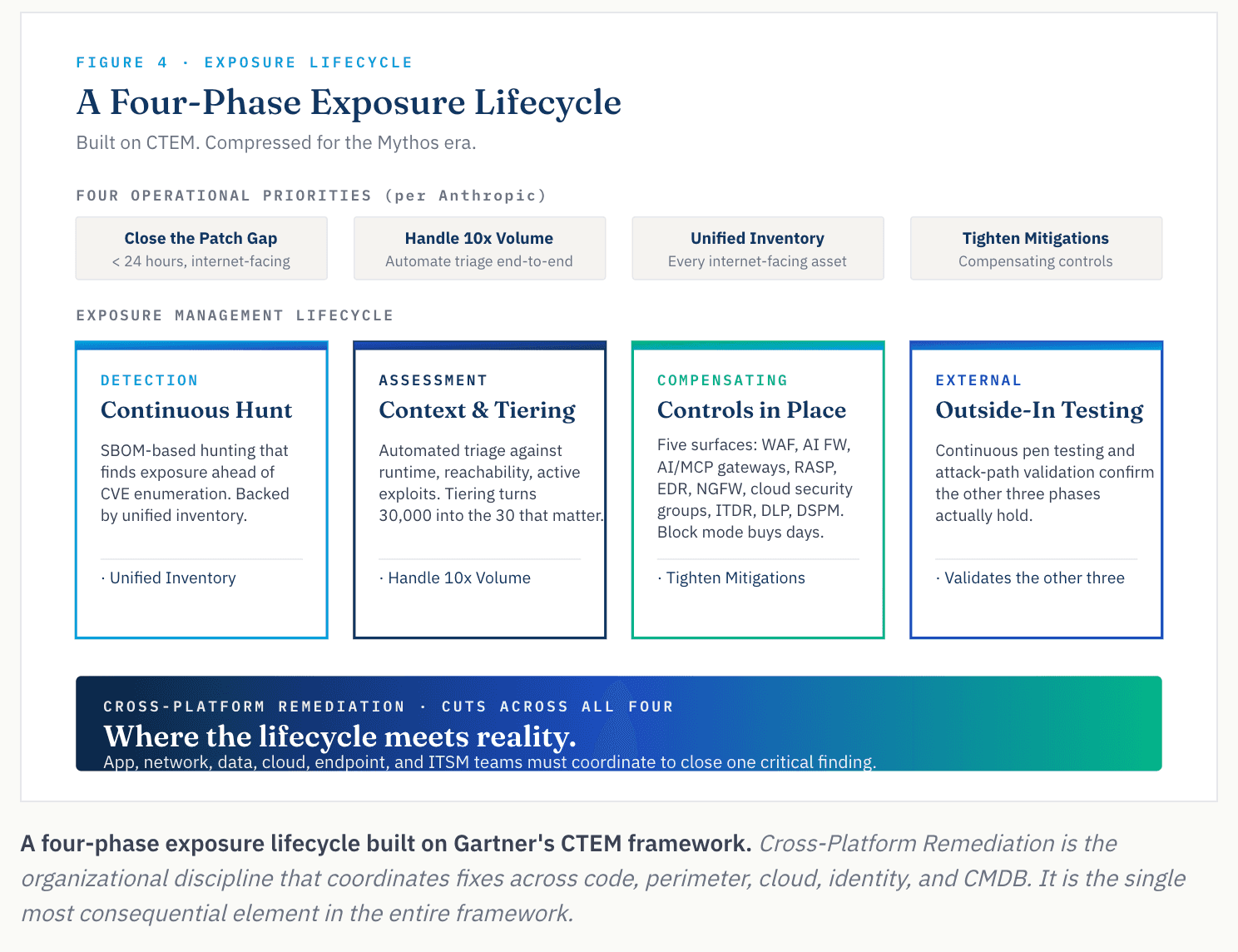
Continuous detection ahead of CVE enumeration
SBOM-based hunting finds exposure before a CVE is formally published: you see the problem before the attacker does. Detection runs on a unified inventory reconciling CMDB, ASM, CSPM, and DSPM. These four sources each see a different slice of your attack surface and rarely agree. Reconcile the feeds you already pay for before investing in new ones.
Attack Surface Management is now required, not optional. ASM continuously discovers internet-facing assets the organization does not know it has: shadow IT subdomains, abandoned cloud accounts, forgotten dev environments. Anything ASM doesn’t see, the adversary will.
Environmental context and application tiering
Automated triage against runtime exposure, internet reachability, active-exploit intelligence, and compensating-control state. The output is the thirty items that matter this week, not the thirty thousand technically open.
Application tiering is the business-context layer most programs don’t apply. A Tier 0 asset (identity providers, domain controllers, crown-jewel databases) tolerates near-zero exposure window. Without this classification, a Tier 0 exposure and a commodity Tier 3 finding compete for the same triage queue.
Use what you have already bought
Most enterprises already own the controls that could mitigate the exposure, but they sit in monitor mode, are misconfigured or untuned, or are shelfware with capabilities that were never operationalized. In enterprise security, compensating controls rarely have an owner. Five surfaces are worth addressing first:
- Infrastructure: NGFW, EDR, microsegmentation, CNAPP, DNS security, cloud security groups.
- Application: WAF, AI firewalls, AI/MCP gateways, RASP, SCA/SAST, CI/CD pipeline gates.
- Identity: ITDR, PAM, conditional access across human and non-human identities.
- Data: Data classification, DLP, DSPM, CASB, tokenization.
- Cyber Recovery: Immutable backups, isolated recovery environments, cyber recovery vaults, tested restore runbooks.
Take Log4Shell as the canonical case. Every enterprise had Java applications they could not remediate on day one. Six compensating controls, none of them remediation, reduced exposure while the patch program caught up:
- WAF rules blocking the
${jndi:}pattern in HTTP requests - EDR rules flagging the Java-to-shell process chain
- Network egress filters blocking outbound LDAP and RMI from application servers
- SCA tooling flagging the vulnerable Log4j version in the build pipeline
- RASP blocking deserialization at runtime
- A single JVM flag disabling the vulnerable feature in some environments
A rule in block mode or a pipeline gate that rejects a vulnerable dependency buys days for teams to plan remediation. In some environments, especially agentic environments, these controls aren’t a bridge to remediation. They are the architecture. We walked through what this looks like in practice in our Lilli breach analysis.
For non-patchable OT environments, the playbook inverts. When you cannot apply preventive controls, shift to detective: passive network monitoring with industrial-protocol deep packet inspection (Dragos, Claroty, Nozomi, Armis) and baseline-anomaly detection on OT protocols.
Independent confirmation that it actually holds
External Validation is outside-in. Continuous pen testing and attack-path validation platforms (Tenzai) test whether reachability claims hold under adversary conditions and whether compensating controls actually block what they claim to block.
A clean internal dashboard paired with a dirty external validation report is one of the most common patterns behind breaches that “shouldn’t have happened.” Run quarterly at minimum, not as a compliance exercise, as an operational one.
Cross-Platform Remediation
Where programs actually fail: A critical web-application CVE may require a code patch from the application team, a WAF rule from the network team, a cloud security group change, an identity rotation, an EDR policy update, and a CMDB update. Each team runs different tools, different change windows, and different SLAs. This is where most enterprise vulnerability management programs break down.
In regulated industries, compression requires legal, audit, and CAB alignment on emergency change paths. In tabletops run with regulated-enterprise clients in late 2025, the existing emergency-change path required between five and fourteen days to patch a critical internet-facing asset. Compressing that path inside 24 hours took six to twelve weeks of cross-functional work. None of those organizations had run the exercise before the CVE forced it.
“30-day patch SLAs on internet-facing assets stopped being a defensible breach response somewhere between Volt Typhoon and Mythos.”
AI for Security within Exposure Management
Five Capabilities That Define AI-Assisted Exposure Management:
- Continuous SBOM-based exposure hunting. Agents evaluate your software bill of materials against threat intelligence ahead of CVE publication.
- Agentic correlation across control state. Agents pull scanner findings, EDR telemetry, WAF rule state, perimeter policy, and cloud network graph into one continuously correlated view, turning 30,000 findings into the 30 that matter.
- Attack-path validation. Agents actively test reachability under adversary conditions rather than inferring it from configuration.
- Supervised autonomous remediation. Agents identify asset ownership and route work items to the right system: Jira for engineering, ServiceNow for IT, Slack for approvals.
- Governance for the agent itself. The agent is a privileged principal in your environment and needs the same controls as any other: defined scope, blast-radius caps, human override, full audit telemetry, and a named human owner.
Shift 02 · Multi-YearSecure Architectures
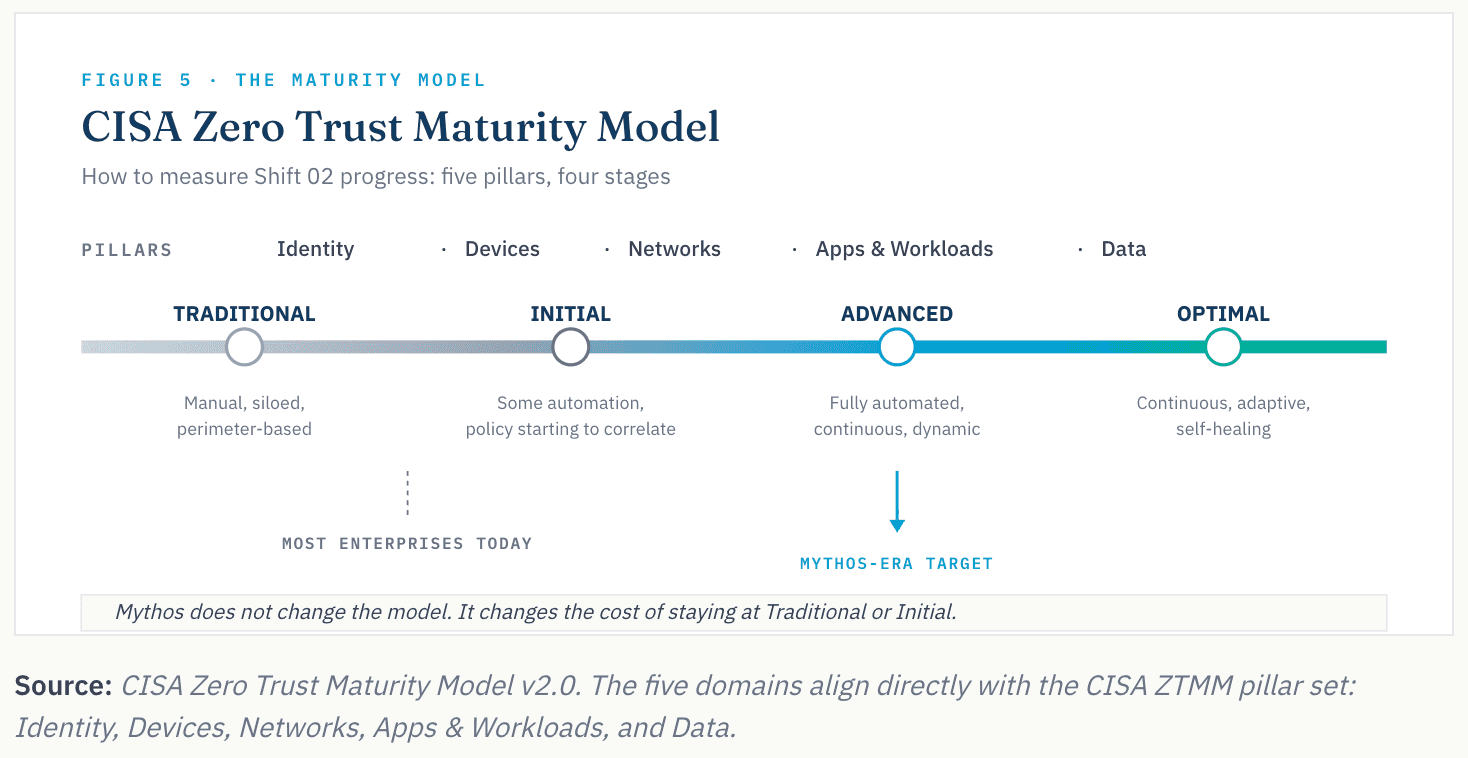
Patching faster is necessary and not sufficient. Mythos forces defense-in-depth, the oldest principle in security architecture, quietly deprioritized across a decade of platform consolidation. Defense-in-depth is the approach. Zero trust is the posture inside it. CISA’s Zero Trust Maturity Model is how to measure progress. Mythos does not change the model; it changes the cost of staying at Traditional or Initial.
Identity
Identity is human, non-human, and agentic. Non-human identities (service accounts, workload identities, API keys, OAuth tokens) outnumber human ones fifty to one in most enterprises. Tokens don’t MFA; they are bearer credentials. Agentic controls that matter now: a non-human identity inventory covering agents alongside services and workloads; short-lived, scope-bound token issuance; and runtime behavioral baselines that treat the agent itself as a monitored principal.
Devices
Device posture is the first access decision. Endpoint compliance signals (patch state, disk encryption, EDR active), mobile device management, and hardware-backed attestation determine whether an authenticated identity actually gets access. IoT and OT endpoints require compensating controls at the network layer.
Networks
SSE and SASE are zero trust expressed at the network layer: identity-aware access with consistent policy across a distributed workforce. Micro-segmentation contains an intrusion to the workload where it began. For OT, which runs 10–18 years and is often unpatchable, the answer is segmentation, detective controls, and ruthless isolation from IT.
Apps & Workloads
Treat each workload as a first-class identity with its own authentication, least-privilege authorization, runtime attestation, and continuous validation. Secure-by-default deployment patterns (infrastructure-as-code with policy guardrails, signed artifacts, immutable images) cost far less than retrofitting security after the fact.
Data
Encryption is table stakes. The harder work is classification at volume, DSPM instrumentation in cloud environments, and treating data flow as a security control rather than a compliance artifact. Egress controls (DLP, CASB) enforce policy at the boundary. An attacker’s objective is usually your data; govern it accordingly.
Shift 03 · Continuous Security Operations
Signature detection cannot keep up with AI-assisted exploitation. The frontier-era SOC has to detect on behavior, not on hashes. Mean time to detect against an attacker who can chain custom exploits in hours decides whether an incident becomes a breach. Mandiant’s 2025 global median dwell time was 14 days. The Mythos-era target is minutes.
Behavioral Analytics
UEBA across human, non-human, and workload identities. A service account that suddenly opens a database connection from a new region is a stronger signal than the equivalent human anomaly; services do not improvise. Identity Threat Detection and Response (ITDR) operationalizes this and belongs in every Mythos-era SOC stack.
Cross-Domain Correlation
Endpoint, network, identity, cloud control plane, and SaaS audit logs in one detection graph mapped to MITRE ATT&CK. The technique-coverage question to track quarterly: which ATT&CK techniques relevant to your threat profile are covered by at least one high-confidence detection across at least two telemetry sources.
Detection Engineering
Detections are code. They live in version control, get reviewed, tested against red team output, and retired when stale. What separates a Mythos-ready SOC from one running on alert tuning is detection-as-code with measurable coverage, false-positive rates, and time-to-detect targets per ATT&CK technique.
Response Automation
Isolate endpoint, revoke token, block egress, disable account, kill workload. Five response actions that should run inside minutes on high-confidence detection without human approval, against a defined set of predicates. Defining those predicates honestly, in tabletop, with legal, with the engineering teams whose workloads might be killed, is the real work.
Detection Velocity · The Gap to Close
Mandiant’s 2025 global median dwell time was 14 days. The Mythos-era target is minutes. Closing that gap is a SOC-modernization program, not a tooling refresh. Measure it quarterly against simulated lateral movement, not against inbox alert counts.
Shift 04 · 6–12 Months: Cyber Resilience
“The attackers are targeting the tools you bought to stop them.” Mandiant M-Trends 2025
Prevention never reaches zero. In a world where frontier-class offensive AI is broadly available, the planning assumption is not if but when. Cyber resilience makes recovery a measurable capability rather than a stated intention: immutable storage no in-band credential can reach, a standby production environment sized to run the business at a Minimum Viable Company level, an isolated environment to bring Tier 0 services back, a clean room for forensics, and a recovery cadence exercised quarterly with identity and virtualization planes in scope.
Tier 0 Dependency Mapping
Most enterprises know which applications are Tier 1. Few have an honest map of the Tier 0 services those applications depend on (Active Directory, DNS, certificate authorities, virtualization control planes, identity providers, secrets managers) and the order they have to come back in. The mapping is the first artifact of a credible recovery program.
Immutable Vault and Isolated Recovery Environment
The vault holds copies that cannot be altered or deleted by an in-band credential, including domain-admin. The Isolated Recovery Environment (IRE) is the segregated infrastructure where those copies become running services. If a domain-admin credential in production can reach either, you do not have a recovery capability; you have a backup.
Standby Production Environment (Minimum Viable Company)
The vault and IRE answer the question of what to restore. The standby production environment answers the question of where to run the business while production is being recovered. If production is ransomed and the IRE is your only target, you are recovering into the crime scene. A fully isolated standby environment, sized and scoped to operate the Minimum Viable Company (the critical processes, customer-facing services, and revenue functions the organization cannot go dark on) is what makes recovery a business continuity event rather than a business interruption. Scope it to MVC, not to full production parity. Full parity is a years-long project. MVC is a scoping decision that can be built and tested in a quarter.
Clean Room
Forensics, malware analysis, and recovery validation happen in a clean room: a separate sterile environment where compromised artifacts can be inspected without re-introducing them to production. Standing one up after the incident is too late. It is a two-quarter build project before one is needed.
Recovery Exercise Discipline
Quarterly exercises against named ransomware scenarios, with identity services and virtualization planes in scope, not just application data. The metric that travels to the board is the trailing four-quarter recovery exercise success rate, not the existence of a runbook. Cyber-insurance carriers increasingly ask for it directly.
Ransomware Now Targets Your Recovery Stack
Per Mandiant M-Trends 2026, the three assets sophisticated ransomware operators target first are (1) identity services, (2) virtualization management planes, and (3) backup infrastructure, the same three you would use to recover from an attack. Resilience planning has to assume all three may be compromised simultaneously.
A Four-Number Scorecard for the Board
Four metrics, one per shift, reported quarterly. These are lag indicators that aggregate the operational work underneath.
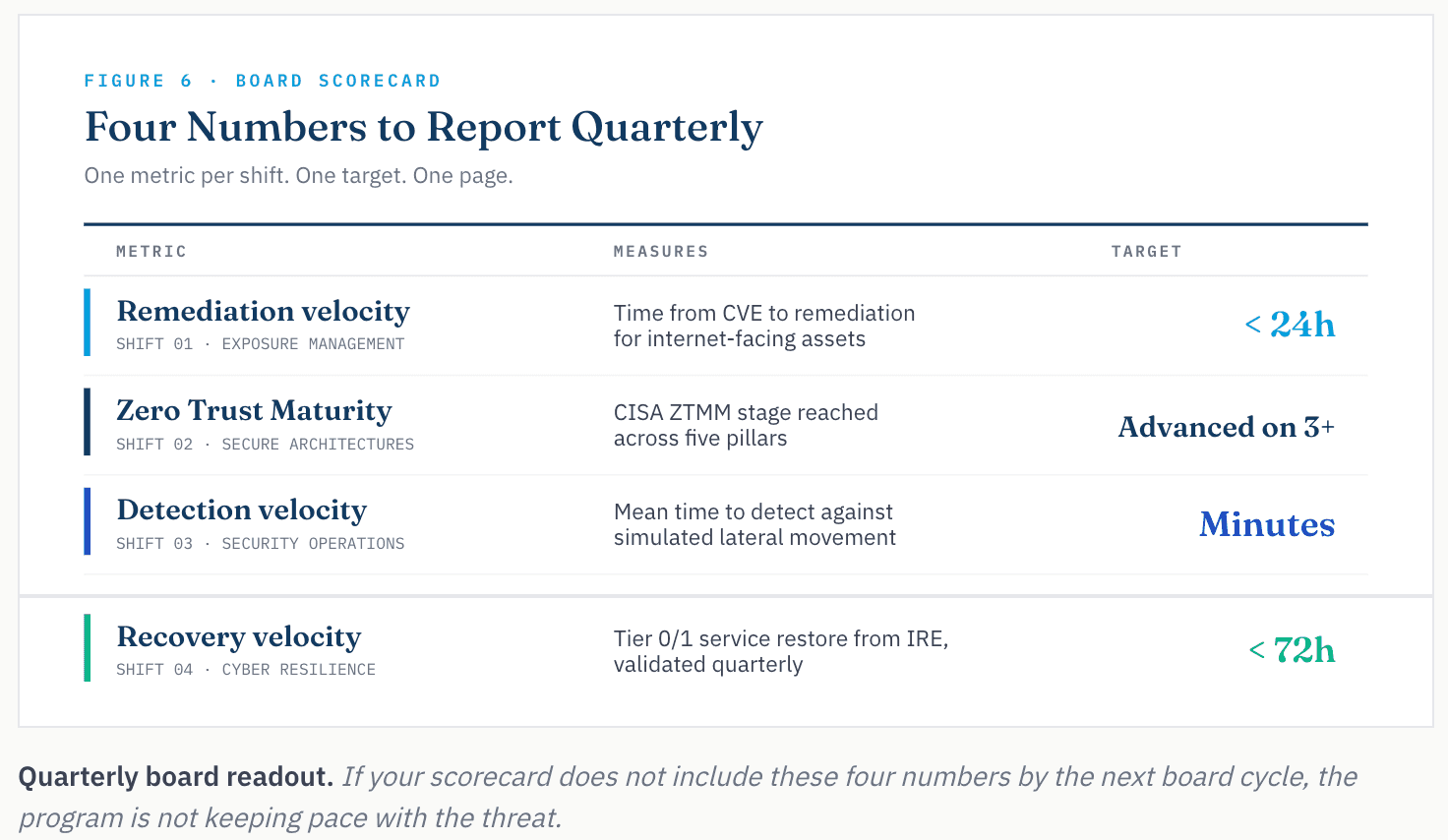
- Exposure finds it first
- Architecture denies reach
- Operations catch the rest
- Resilience holds the line
◆ One Question for Monday’s Leadership Meeting
If a frontier-class capability was pointed at your environment this week, what would fail first, and what would fail next?
That answer is where your program starts.
Where AHEAD Engages
AI for security threads through all four engagements below as the operational execution layer. The outcomes show up in faster remediation on Exposure Management and faster detection on Security Operations, with supervised-autonomous remediation as the longer horizon.
Exposure Management
AHEAD’s Sightline Program runs the four-phase lifecycle as a six-to-twelve-month engagement with your team. We bring the cross-domain remediation bench. The discipline gets built on your staff, not parked on ours.
Outcomes we drive and track:
- Remediation velocity under 24 hours on internet-facing assets
- Compensating-control coverage above 70% on critical CVEs
- Reachability-validated finding ratio: signal versus noise
Secure Architectures
Our Zero Trust Advisory practice runs against the CISA ZTMM. Current state, target state, sequenced roadmap by blast-radius reduction. We measure quarterly.
Outcomes we drive and track:
- Advanced ZTMM rating on three or more pillars within twelve months
- Standing-privilege identity reduction quarter over quarter
- Lateral-movement containment time in tabletop simulation
Security Operations
Our SOC Modernization practice starts with what you already run. SIEM, SOAR, XDR, and threat intel get inventoried against a capability requirements list. Behavioral analytics and ATT&CK-aligned correlation come in next, not first.
Outcomes we drive and track:
- Mean time to detect in minutes against simulated lateral movement
- Mean time to respond on high-confidence detections
- MITRE ATT&CK technique coverage relevant to your threat profile
Cyber Resilience
Our Cyber Recovery practice starts with the Tier 0 dependency map most enterprises do not have. We build the immutable vault and the IRE around those services. Quarterly recovery exercises include identity and virtualization planes, not just application data.
Outcomes we drive and track:
- Tier 0 and Tier 1 service recovery within 72 hours
- Immutable vault unreachable from production domain-admin credential
- Recovery-exercise success rate over trailing four quarters
Sources
- Anthropic, Claude Mythos Preview red team report
- Anthropic, Claude Mythos Preview system card (244-page document)
- Anthropic, Project Glasswing announcement
- UC Berkeley, Wang et al., CyberGym: Evaluating AI Agents’ Real-World Cybersecurity Capabilities at Scale (arXiv:2506.02548)
- OpenAI, Introducing GPT-5.5 (April 23, 2026)
- AISLE, AI Cybersecurity After Mythos: The Jagged Frontier (Stanislav Fort, April 8, 2026)
- Cloud Security Alliance, SANS Institute, OWASP Gen AI Security Project, Building a Mythos-ready Security Program (April 12, 2026)
- Bloomberg, Anthropic’s Mythos model accessed by unauthorized users
- Daniel Stenberg, daniel.haxx.se, cURL submission-rate data and bug bounty program closure
- Mandiant, M-Trends 2025 and M-Trends 2026 annual reports
- Google Threat Intelligence Group, 2025 zero-day exploitation analysis
- CISA, Zero Trust Maturity Model v2.0
- CyberSeek.org, cybersecurity workforce supply/demand data (514,000 unfilled U.S. positions)
About the author
Felix Vargas
Senior Director, Specialist Solution Engineering
Felix Vargas is a senior leader in AHEAD’s security practice, advising enterprises on modernizing their defenses across cloud, data center and AI-powered environments. He specializes in zero trust architecture, secure-by-design infrastructure and aligning cybersecurity strategy with business outcomes, and frequently works with customers building on NVIDIA technologies. Felix has more than 15 years of experience helping organizations reduce risk while accelerating innovation, and is a regular speaker on emerging threats, AI security, and the future of cyber resilience.

 ;
; ;
; ;
;